--Originally published at Hermes's Blog
One of the most terryfing things in cybersecurity is not our private data being leaked. Imagine our own health is compromised our healthcare data from an hospital is leaked, or even that some critical devices in our bodies could be manipulated remotely by others.

A Bayer MedRad device used to assist in MRI scans infected with the WannaCry ransomware from Forbes.
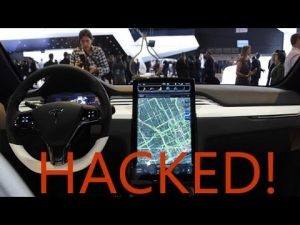
Past year, when the WannaCry ransomware was a thing, some hospital networks were infected, causing hospitals to close their doors to new patients and halting treatments for other patients because they were not able to access the patient’s data records. A lot of healthcare data is being stored in the cloud, this has a expected growth rate of 20.5% by 2020, this is such a risk because, data in the cloud must be correctly protected, it requires robust encryption measures and appropiate authentication. 90% of hospitals run legacy applications to preserve patients data, these kind of applications can have serious security holes that a cybercriminal could take advantage of, they run old and unpatched operating systems (Causing the WannaCry infection).
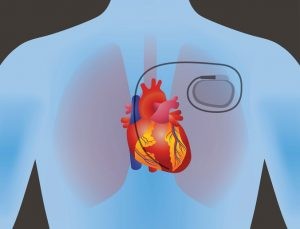
Last year, St Jude Medical’s pacemakers had a security scandal. It turns out that half a million of patients’ pacemakers could be hacked to run the batteries out or even alter the patient’s heartbeat. The manufactured issued a firmware update (ha! an update for your heart, isn’t that cool?). They are all radio-controlled implantable cardiac pacemakers. The FDA (Food and Drug Administration agency) says that the vulnerability allows an unauthorised user to access a device using commercially available equipment and reprogram it, this could lead to the death of the patient. The security weakness was discovered by MedSec, a cybersecurity firm that specialises in researching vulnerabilities in the medical devices and healthcare industries, and it had previously been the target of a lawsuit from SJM for disclosing such vulnerabilities. It turns out that St Jude Medical knew about this vulnerability since 2014, but did not took action until the weakness was make public. You can read more about here, the story is great, with lots of plot twists.
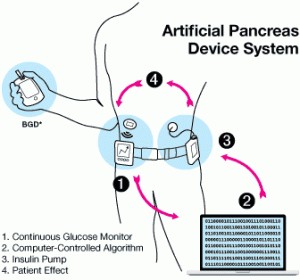
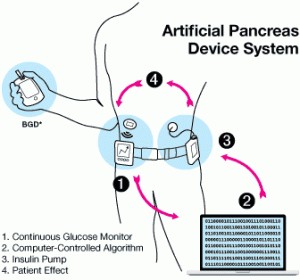
Another device that might be a source of security scandals in the future is the artificial pancreas system, this thing is an IOT insuline monitor glucose monitor that comunicates with an insuline pump and a computer (like a raspeberry pi) via radio waves. There is even an open source project that lets you create your own system called OpenAPS.
Sources
http://resources.infosecinstitute.com/top-10-threats-healthcare-security/
https://www.theguardian.com/technology/2017/aug/31/hacking-risk-recall-pacemakers-patient-death-fears-fda-firmware-update