--Originally published at Mental Droppings of a Tired Student
Hacking has been a popular topic for a long time, especially since the 90s and Hollywood’s fantasy of grungy goth looking teenagers doubling as computer geniuses having the world literally at their fingertips. In their portrayal of hacking, a hacker is kind of like a magician able to control every technology imaginable through a computer though realistically that is not how things work at all. You gotta admit controlling every TV in the globe through a computer? Far fetched to say the least, not to mention extremely laughable. Or perhaps the computer geeks should be flattered that the normies think so highly of their skills? Who knows…

So there are two contrasts to hacking, righteous, ethical, white hat goody-two-shoes hacking and black hat, bad apple of the bunch, scum of the earth hacking. Of course there are those who fancy themselves “grey hat hackers”, but I think such distinction is unnecessary.

White hat hackers are those who are ethical and do things like diagnosing security flaws in order to prompt corporations to fix them. Black hat hackers commit cyber crimes for financial gain or simply because they want to watch the world burn… you know, for the lulz.
Let’s traverse this topic in an orderly fashion: from dark to light. You know, just so no one gets offended because apparently there are more than two shades of hacker hats. Let’s use a scale to categorise each of these hackers, god I love quantifying things! It gives me solace in a world full of chaos. I’m using D&D alignments as a base because I have no shame.
- Neutral Good: Finds security flaws, is completely altruistic in their hacking, finds a major flaw that affects many systems or donates their earnings.
- Chaotic Good: Finds security flaws and notified the company, got a reward for








 .
.
- Chaotic Neutral: Generally a young hacker exploring his or her skills. Or an experienced hacker who committed a cyber crime but eventually turned to the light side as a consultant at a company or something of the sort.
- Neutral Evil: Committed a cyber crime for personal financial gain, stole information and sold it, intended to harm others.
- Chaotic Evil: Those who hack for the lulz or expose not only companies but regular users to danger.
After all there is no point in explaining one thing without the other, contrast is often a necessity of life. How else would we know right from wrong?
Matthew “Kuji” Bevan & Richard “Datastream Cowboy” Pryce

Category: 5
Backstory:
These two hackers are said to have “nearly started a third world war” according to Supervisory Special Agent Jim Christy, at the time working for the Air Force Office of Special Investigations. That’s right, they were nearly responsible for countless deaths and collateral damage.
This duo of British hackers sure gave the U.S. government a run for their money when they gained access to sensitive USAF, NASA, and NATO establishments back in 1994. They copied battlefield simulations from Griffiss Air Force Base in New York, intercepted messages from U.S. agents in North Korea, and gained access into a Korean nuclear facility.
To sum up the risks and concerns brought about by their hacking, Datastream Cowboy (what a cheesy name) , then 16 years old, presumably being tutored by Kuji who was then only 21, hacked his way into a research facility in Korea, and dumped the contents of the Korean Atomic Research Institute’s database on the USAF system. The concern was that if North Korea noticed, they would think the transfer of data was an intrusion by the U.S Air Force, and threaten physical retaliation for the espionage; fortunately it turned out to be South Korean data, significantly less volatile… right Kim Il-sung? That would have definitely triggered a heart attack hahaha… oops
Gary Mckinnon, the scot who got away

Category: 5
Gary “Solo” Mckinnon hacked into 97 United States military and NASA computers over a 13-month period between February 2001 and March 2002.
The US authorities stated he deleted critical files from operating systems, which shut down the United States Army’s Military District of Washington network of 2,000 computers for 24 hours. McKinnon also posted a notice on the military’s website: “Your security is crap”. He’s riding on a high horse for someone who, you know, got caught? He also attempted to cover his tracks by connecting from his girlfriend’s aunt’s house, that’s just genious. After the September 11 attacks in 2001, he deleted weapons logs at the Earle Naval Weapons Station, rendering its network of 300 computers inoperable and paralyzing munitions supply deliveries for the US Navy’s Atlantic Fleet. McKinnon was also accused of copying data, account files and passwords onto his own computer. US authorities stated the cost of tracking and correcting the problems he caused was over $700,000.
In 2012 it was decided that he would not face charges in the UK, nor would he be extradited to the U.S. to face charges there. That wasn’t very nice of the U.K. and this hardly encourages affection between the two countries, I guess they’re salty given the history between the two.

Jeanson James Ancheta A.K.A Resilient

Category: 4
This is probably the most gangsta hacker of the bunch. He bought a BMW with his hacking earnings, very GTA if you ask me. This California native became the first hacker to be charged with controlling an army of hijacked computers dubbed botnets to send large quantities of spam across the Internet. He used the worm “rxbot” in 2004 to take control of 500,000 computers (which included U.S. military computers) and used their combined strength to take down major sites. So like a DOS attack. He then put out ads for his services, and offered clients the opportunity to take down any website they wanted, for a price. Ancheta was caught in 2005 when one of his clients turned out to be an undercover FBI agent. He had to give up the $58,000 he made from hacking, pay back $16,000, give up his BMW, and serve 60 months in prison.
Astra (real name withheld to media)
Category: 4

Astra is an 58-year-old Greek mathematician ( If you ask me he is like the Arquimides of hackers) who hacked into the computer systems of a French comany named Dassault Group over a period of five years, stealing weapons technology data and 3D modeling software that he then sold to at least 250 people in Brazil, France, Germany, Italy, South Africa, and the Middle East. Dassault was understandably pissed, and went on a global manhunt that tracked ASTRA to an Athens apartment. ASTRA was caught in January 2008 and is serving six years in jail. It’s still a mystery why Dassault chose not to disclose his name.
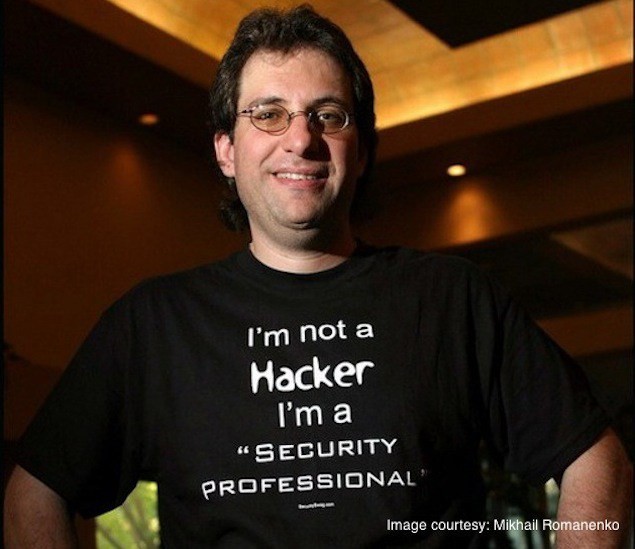
Kevin Mitnick
Category: 3
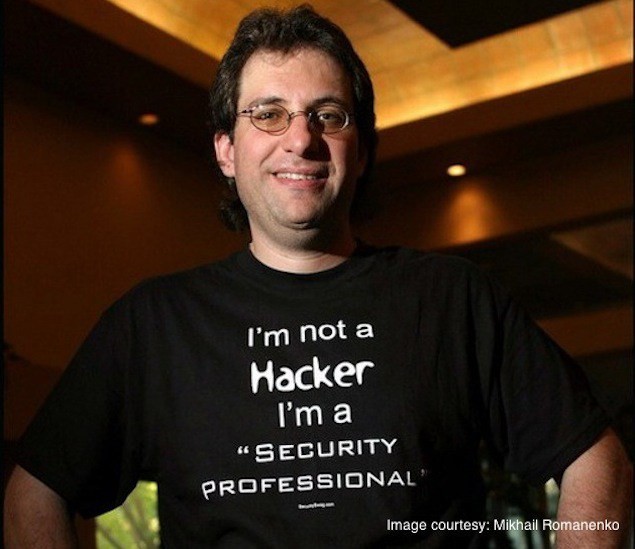 An infamous hacker, he had a good run but after a well-publicized pursuit, the FBI arrested Mitnick on federal offenses related to a 2 and a half-year rampage of computer hacking which included computer and wire fraud. He was found with cloned cellular phones, more than 100 clone cellular phone codes, and multiple pieces of false identification.
An infamous hacker, he had a good run but after a well-publicized pursuit, the FBI arrested Mitnick on federal offenses related to a 2 and a half-year rampage of computer hacking which included computer and wire fraud. He was found with cloned cellular phones, more than 100 clone cellular phone codes, and multiple pieces of false identification.
Mitnick served five years in prison. He was released on January 21, 2000. He was initially forbidden to use any communications technology other than a landline telephone. Mitnick fought this decision in court, eventually winning a ruling in his favor, allowing him to access the Internet. Under the plea deal, Mitnick was also prohibited from profiting from films or books based on his criminal activity for seven years, under a special judicial Son of Sam law variation.
He fancies himself a “social engineer” rather than a hacker, but yeah let’s be real here, he is simply a hacker. He gets category 3 for turning his hacking skills into a contribution to society since he now runs Mitnick Security Consulting LLC, a computer security consultancy and is part owner of KnowBe4, provider of an integrated platform for security awareness training and simulated phishing testing.
Michael “Mafiaboy” Calce
Category: 3
 In 2000, a high school student named Michael Calce, who went by the online handle Mafiaboy, brought down the websites of Amazon, CNN, Dell, E*Trade, eBay, and Yahoo!. At the time, Yahoo! was the biggest search engine in the world. Mind you he was only 15 at the time and had the New York Stock Exchange running around like chickens with their heads cut off. At this point they probably deserved to be hacked.
In 2000, a high school student named Michael Calce, who went by the online handle Mafiaboy, brought down the websites of Amazon, CNN, Dell, E*Trade, eBay, and Yahoo!. At the time, Yahoo! was the biggest search engine in the world. Mind you he was only 15 at the time and had the New York Stock Exchange running around like chickens with their heads cut off. At this point they probably deserved to be hacked.
In 2000, he provoked a DOS attack using a handful of university networks, harnessing their combined computing power to attack the websites listed before. His attack is child’s play nowadays, but back then in was a pretty flashy move and gained him the notoriety he seemed to want from his hacker buddies. “The overall purpose was to intimidate other hacker groups,” says Calce. Back then, he says, “the whole of the hacking community was all about notoriety and exploration, whereas you look at hackers today and it’s all about monetization.”
Unfortunately president Clinton wanted to make an example of him and the stunt he pulled. He was charged with more than 50 crimes and eventually sentenced to eight months in a youth group home.
Today, Calce is what’s called a white hat hacker, his mafia days are over. Companies hire him to help identify security flaws in their systems and design better security features. Looking back, he thinks some good did come from the attack he launched. “It raised a lot of issues,” he says. “It definitely advanced and created a pretty big focus on security, and the problems and inherent flaws that come with computers and internet.”
Sergey Glazunen, from Russia with love
Category: 2
 In 2012 Google launched Pwnium, a competition for hackers to find security exploits in Chromer. Chromium contributor Sergey Glazunov submitted the first successful entry to the Pwnium contest, revealing a “Full Chrome Exploit” that bypassed the browser’s sandboxing security. The exploit makes it possible for a malicious hacker to do just about anything they want on an infected machine. Glazunov was able to execute “code with full permission of the logged-on user.” Schuh called the feat “impressive,” and said that it deserved the $60,000 bounty.
In 2012 Google launched Pwnium, a competition for hackers to find security exploits in Chromer. Chromium contributor Sergey Glazunov submitted the first successful entry to the Pwnium contest, revealing a “Full Chrome Exploit” that bypassed the browser’s sandboxing security. The exploit makes it possible for a malicious hacker to do just about anything they want on an infected machine. Glazunov was able to execute “code with full permission of the logged-on user.” Schuh called the feat “impressive,” and said that it deserved the $60,000 bounty.
This discovery enabled Google to work on a fix and avoid countless disasters that could have ensued from that security flaw. By participating in an ethical form of hacking, Sergey contributed to the greater good of users and also made a pretty penny. Pretty neat if you ask me.
Pinkie Pie the fearless pony
Category: 2
 Pinkie Pie is a character from the children’s terrifying TV show My Little Pony, created by Lauren Faust, who is a huge Trekkie by the way. The character is known for being a wildcard, a chaotic character who uses humor as a balm to soothe any troubling situation, this pony represents the element of laughter. It’s difficult to know why this hacker chose this particular pony as his online handle name, the only relation between ponies and hacking is the term “pwning”.
Pinkie Pie is a character from the children’s terrifying TV show My Little Pony, created by Lauren Faust, who is a huge Trekkie by the way. The character is known for being a wildcard, a chaotic character who uses humor as a balm to soothe any troubling situation, this pony represents the element of laughter. It’s difficult to know why this hacker chose this particular pony as his online handle name, the only relation between ponies and hacking is the term “pwning”.
Pinkie Pie has shown consistently amazing skills in exploiting Chrome vulnerabilities. Between years 2012 and 2013 Pinkie Pie earned $150,000 for his ability to continuously give Google Chrome developers security nightmares about their browser being profaned by a magical pink pony.
Pinkie Pie is a formidable security expert, his skill is apparent in the fact that Chrome has a robust sandboxing mechanism, getting through it’s defenses is no walk in the park, and yet this fearless pony has been able to exploit Chrome on multiple occasions. In any case, Pinkie Pie has definitely earned his cutie mark within the ethical hacking community.
Sanmay Ved, Once the owner of google!
Category: 1
 Honestly, this category was made for Sanmay. This curious hacker was learning more about the Google Domains interface a 1:20 in the morning, he typed in google.com and clicked search domains, Google.com was available.
Honestly, this category was made for Sanmay. This curious hacker was learning more about the Google Domains interface a 1:20 in the morning, he typed in google.com and clicked search domains, Google.com was available.
He purchased the domain successfully, eventually he was contacted by Google and offered him what must have been a big reward.
“Per my request, they will now donate the reward amount (they have doubled the amount as it is now going to charity) to the Art of Living India foundation. I have chosen that the donation be made towards the Art of Living’s education program which runs 404 free schools across 18 states of India, providing free education to more than 39,200 children in the slum, tribal and rural belts where child labor and poverty are widespread. The schools nurture the complete child, including body, mind and spirit.
In the interest of protecting Google, I do not wish to discuss the particulars of their final finding, and the reward amount.” Says Sanmay within his linked in article where he explains this wild tale. I will link it below it’s a very good read.
Needless to say Sanmay is truly a nice guy and the epitome of what ethical hacking should be. I have to admit I wouldn’t have so readily donated the reward, it takes a very selfless person to do that. #FaithInHumanityRestored
I hereby end our journey trough the ranks of all hackers and their alignment. Let these stories serve as cautionary tales or inspiration for your adventured through out the world of hacking. Happy hacking folks!
References:
https://en.wikipedia.org/wiki/Mathew_Bevan
https://www.nimbushosting.co.uk/ethical-hackers/
https://www.youtube.com/watch?v=-XpPEmcnKCk
https://en.wikipedia.org/wiki/Gary_McKinnon
http://www.complex.com/pop-culture/2012/02/the-8-best-computer-hackers-of-all-time/3
https://en.wikipedia.org/wiki/Kevin_Mitnick
http://www.livehacking.com/tag/sergey-glazunov/
http://www.eweek.com/blogs/security-watch/pinkie-pie-and-his-google-exploits-the-legend-grows.html
https://www.linkedin.com/pulse/i-purchased-domain-googlecom-via-google-domains-sanmay-ved


