--Originally published at #TC2027 #CParravirgen
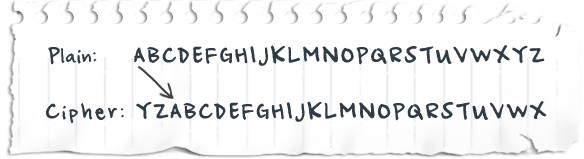
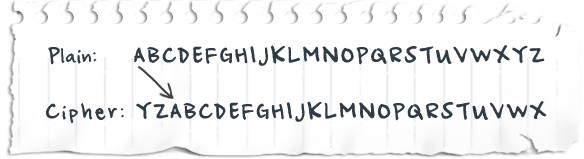
Hardware VS Software
There are some kinds of HW encryption…
Whole disk, this refers to the encryption of an entire physical or logical disk. While this is currently done mostly in software, hardware based disk encryption is a growing technology which is expected to surpass software products for whole disk encryption over the next few years.
This form of encryption secures the entire content of a disk or volume and decrypts/encrypts it during use after a key has been given. It would not protect the information if you send it over the network…
but it helps if you lost it!
Now let’s get into some heavy technical encryption. Let’s talk about PGP.
PGP combines some of the best features of both conventional and public key cryptography. PGP is a hybrid cryptosystem.
PGP then creates a session key, which is a one-time-only secret key. This key is a random number generated from the random movements of your mouse and the keystrokes you type. This session key works with a very secure, fast conventional encryption algorithm to encrypt the plaintext; the result is ciphertext. Once the data is encrypted, the session key is then encrypted to the recipient’s public key. This public key-encrypted session key is transmitted along with the ciphertext to the recipient.
Keys are stored in encrypted form. PGP stores the keys in two files on your hard disk; one for public keys and one for private keys. These files are called keyrings. As you use PGP, you will typically add the public keys of your recipients to your public keyring. Your private keys are stored on your private keyring. If you lose your private keyring, you will be unable to decrypt any information encrypted to keys on that ring.
A digital certificate consists of three things: