--Originally published at The shield of the world
Let´s talk about the CIA and not, this is not a post related to some Tom Clancy book or movie or whatever…

Yeah…CIA, we are talking about Information Security and when we refer to CIA in information security we are talking about Confidentiality, Integrity and Availability. Which are like the holy trinity.
And this is because all information security try to achieve at least one of these three.
- Protection of confidentiality of data
- Preserve the integrity of data
- Promote the availability of data for authorized use
And we are gonna talk a little bit more about each of these main goals in information security.
Confidentiality
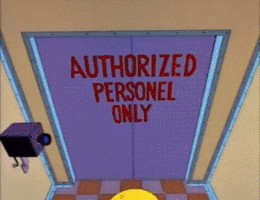
We could say that confidentiality is like privacy… we need to protect the information from people that should not be reading, playing, or doing anything with information that is not related to them. But we need to ensure that the correct people can have access to this information. Access must be restricted like the clubs when they choose who is going to enter and who is not. Data is usually in larger companies categorized according to the amount and type of damage that could be done if it falls into unintended hands.
Some methods to make the data available to the right people are usernames and password, encryption and some biometric verification, reading the retina or fingerprint. Also security tokens, key fobs or soft tokens. Keybase is a cool form of getting in touch with people and to share information encrypted to ensure that only them can decrypt and read it.
Integrity
This involve maintaining the constancy, accuracy and trustworthiness of data over its entire life cycle… yeah, when you tell the teacher or anyone look I have not changed this file look at the date obviously I haven’t change it, yes you can. So








