--Originally published at (Not so) Random talk
Wrecking stuff have always been Ralph’s thing. Ever since his tree stump was moved to the dumpster, he had dedicated himself to wreck the building that was built in his old place. But, whenever Wrack starts wrecking, Felix Jr. has always been there to fix things, thankfully. With his useful hammer, he always fixes the windows and reconstructs the zones Ralph has broken with his big fists. And time and time again, our hero manages to fix everything, get a golden medal, and leave the villain in the mud.

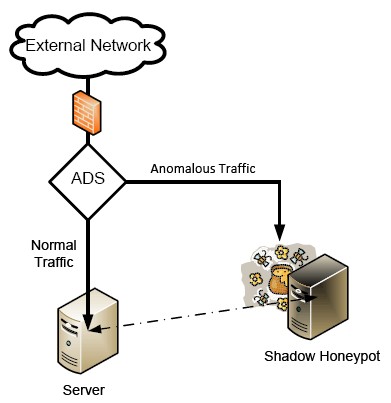
However, times change. And just when Ralph was resigning himself, some interesting trash got into the dumpster. It was lot of information about networking that the Highlanders decided wasn’t important when setting their new networks. And with it, Ralph also learned how to attack this new thing called network. Yes, Wreck it Ralph is now Wrecking the Network! Now in a hurry, Felix had to learn about security networks and dive into the practice of protecting the usability and integrity of your network and data of the Highlanders. Set into this new adventure with Felix, and fix all the things that Ralph has damaged as well as setting up the new multiple layers of defenses on the network.

The way of playing in this game is somewhat different that in the other installment. In each level, you must ensure or do activities that conform network security. Earn a certain number of points to advance to the next level. These activities are:
Wireless Security: set up the wireless security for the Highlanders network, which they used to have on default and Its probably one of the ways in which Ralph accessed the network. To do so in a basic level, change the passwords on the modems of the Highlanders.
Network isolation: divide