--Originally published at (Not so) Random talk
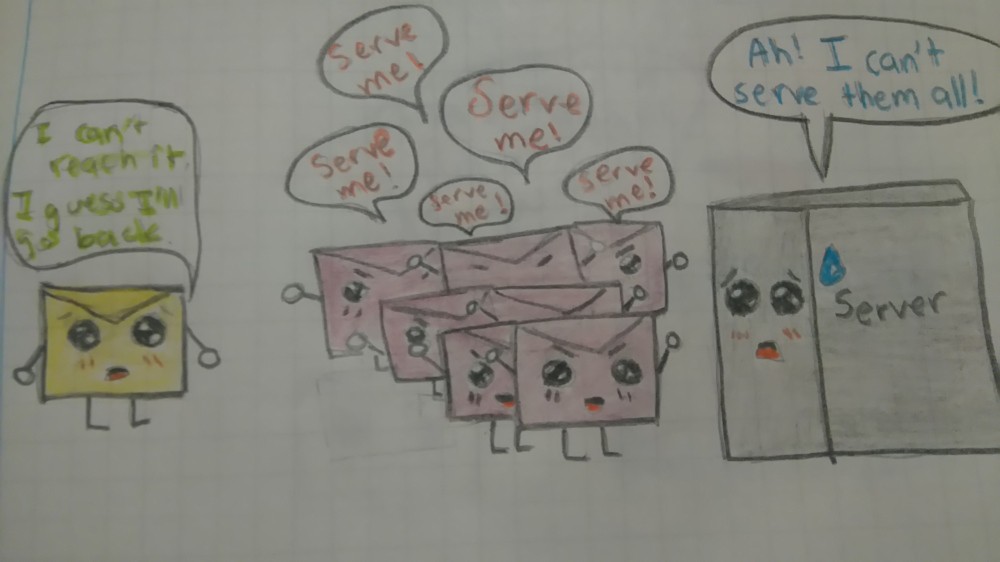
The network can be a Universe of its own. Vast, full of things that are or can be unknown. And just like in Sci-Fi movies, it is plagued with dangers. Hackers, malware, etc. Everything is there. As like in some movies, you need to learn to protect yourself. If not, you might be just like those victims, getting eaten by that unknown thing.
I’ve already mentioned the basics some, if not many times, in the past, but here they come again, plus some new tips in order to browse safely, dearly from me to you:
Update your browser
Everyday thing: Have an antivirus or antimalware and keep it updated too, obviously.
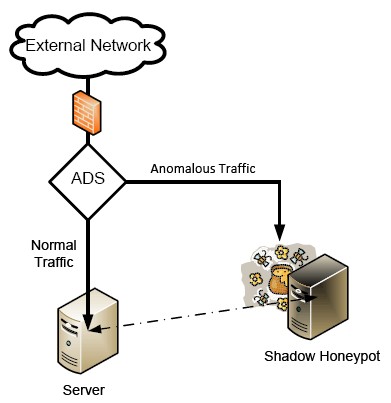
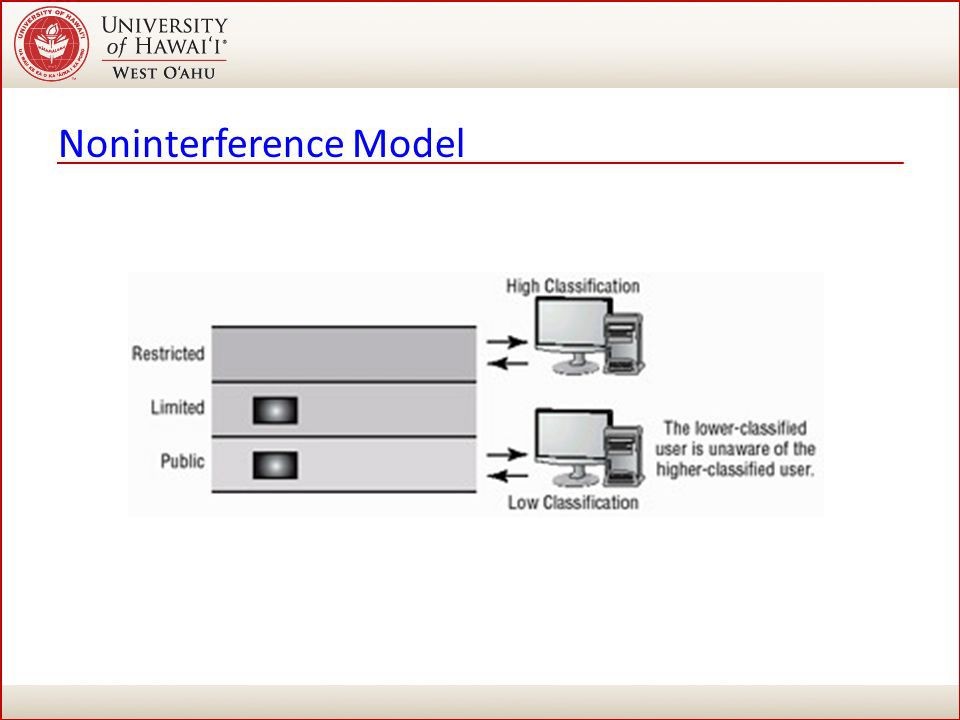
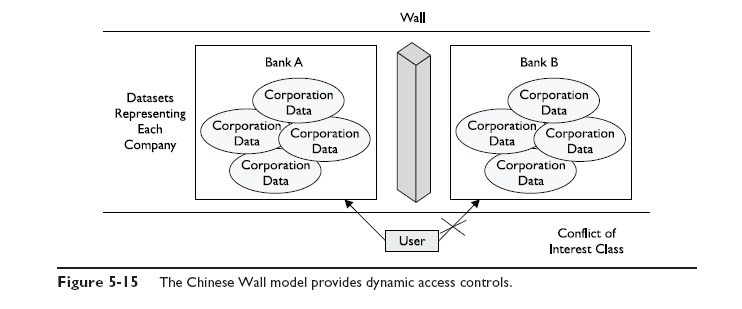
Basic protection: Use firewall if you are not on an expertise level please do not lower firewall. Your computer comes with firewall by default and it helps you filter bad stuff from the web (want to learn more about it read my past post).
Not everything clickable should be clicked: really, just don’t. If something popups, mostly common in not very safe sites, don’t click on it, close it immediately. Those can be gateways for the alien to filter into your spaceship.

Public doesn´t equal good: Don’t go into public open networks without some sort of security, or even better, don’t get on them at all. By doing so, you are probably literally leaving your info in the air for someone to grab it.
Buy smart, buy safe: Just do online shopping from trusted and well recognized sites, preferably using platforms like Paypal.
Free software can come with a price: not all software out there is good, that’s why you should only download / install certified software.
If your browser recommends you against it, don’t insist: Don’t play with fire. If your browser is already doubting on