--Originally published at The shield of the world
Let´s talk about the CIA and not, this is not a post related to some Tom Clancy book or movie or whatever…

Yeah…CIA, we are talking about Information Security and when we refer to CIA in information security we are talking about Confidentiality, Integrity and Availability. Which are like the holy trinity.
And this is because all information security try to achieve at least one of these three.
- Protection of confidentiality of data
- Preserve the integrity of data
- Promote the availability of data for authorized use
And we are gonna talk a little bit more about each of these main goals in information security.
Confidentiality
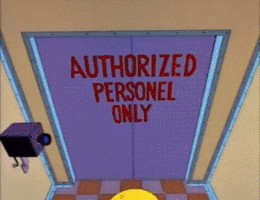
We could say that confidentiality is like privacy… we need to protect the information from people that should not be reading, playing, or doing anything with information that is not related to them. But we need to ensure that the correct people can have access to this information. Access must be restricted like the clubs when they choose who is going to enter and who is not. Data is usually in larger companies categorized according to the amount and type of damage that could be done if it falls into unintended hands.
Some methods to make the data available to the right people are usernames and password, encryption and some biometric verification, reading the retina or fingerprint. Also security tokens, key fobs or soft tokens. Keybase is a cool form of getting in touch with people and to share information encrypted to ensure that only them can decrypt and read it.
Integrity
This involve maintaining the constancy, accuracy and trustworthiness of data over its entire life cycle… yeah, when you tell the teacher or anyone look I have not changed this file look at the date obviously I haven’t change it, yes you can. So




Data must not be changed in transit, and steps must be taken to ensure that data cannot be altered by unauthorized people. The measures also include file permissions and user control. But a really cool feature is when you use GPG to actually sign some file. Then you can verify the sign that the file has with your sign. You can modify something on the file save it and verify the sign again and it will tell you that the signs doesn’t match.
Also the gits are very used in programming, because you have versions of the code so if you know that a version works and someone modify something and now nothing is working, you can come back to an earlier version.

Availability
And the last one of these, availability of information refers to ensuring that authorized parties are able to access the information when needed. This means maintaining all the hardware fully functional, performing repairs when needed and keeping the OS environment without SW conflicts.
Keeping the bandwidth needed to maintain a good communication without bottlenecks. Redundancy, failover, RAID even high-availability clusters can mitigate serious consequences when hardware issues do occur.
Safeguard against data loss or interruptions in connections are other ways of failing in the availability of data. We need a backup of the important information and must be located in a geographically isolated location if the information is like max level for a big company. Even avoid DoS which we have already talked is a good way of keeping the data available.

But, there are some special challenges for CIA or AIC which is another way of calling these three main goals.
Big data, IoT privacy and IoT security is the next big challenge for CIA as the amount of data to take care is too high! All the possible devices connected sending information is just ridiculous. The projections are that each people will have 7 devices connected or “smart devices” …I think that my belt will tell me when to stop eating haha
That’s all for now folks!! Take care and protect yourselves!

http://whatis.techtarget.com/definition/Confidentiality-integrity-and-availability-CIA


